Loading...
Searching...
No Matches
#include <stdio.h>#include <stdlib.h>#include <time.h>#include "secp256k1.c"#include "../include/secp256k1.h"#include "assumptions.h"#include "group.h"#include "testrand_impl.h"#include "ecmult_compute_table_impl.h"#include "ecmult_gen_compute_table_impl.h"
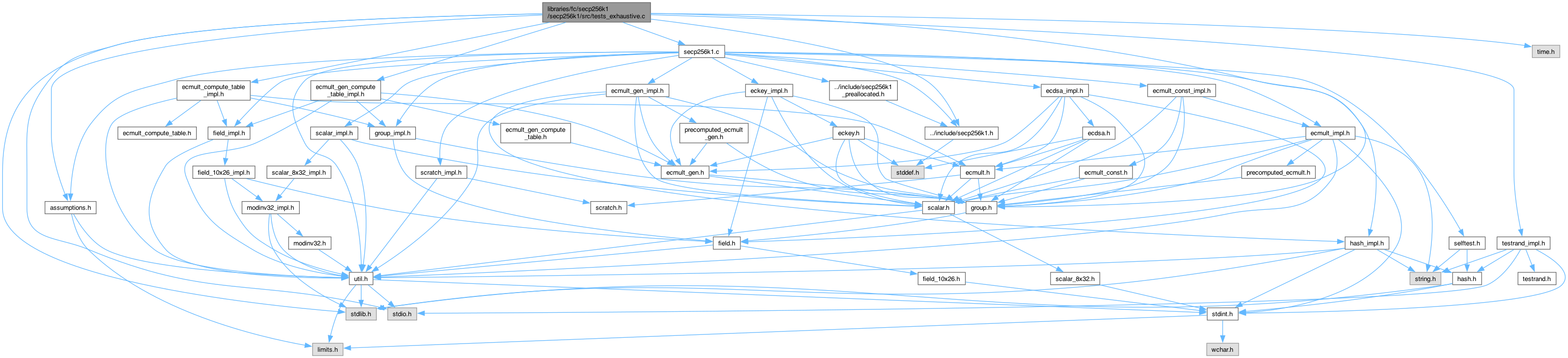
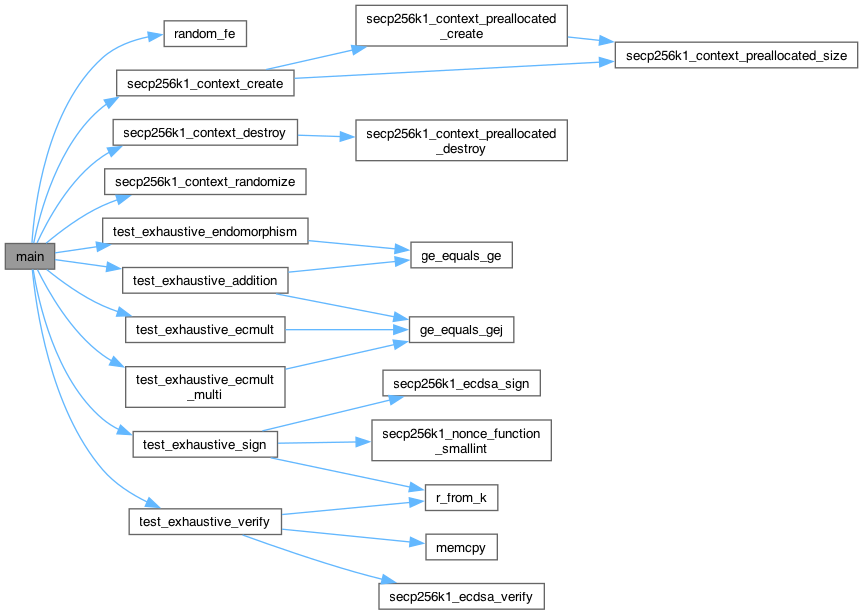
Include dependency graph for tests_exhaustive.c:
Go to the source code of this file.
Classes | |
| struct | ecmult_multi_data |
Macros | |
| #define | EXHAUSTIVE_TEST_ORDER 13 |
Functions | |
| void | ge_equals_ge (const secp256k1_ge *a, const secp256k1_ge *b) |
| void | ge_equals_gej (const secp256k1_ge *a, const secp256k1_gej *b) |
| void | random_fe (secp256k1_fe *x) |
| int | secp256k1_nonce_function_smallint (unsigned char *nonce32, const unsigned char *msg32, const unsigned char *key32, const unsigned char *algo16, void *data, unsigned int attempt) |
| void | test_exhaustive_endomorphism (const secp256k1_ge *group) |
| void | test_exhaustive_addition (const secp256k1_ge *group, const secp256k1_gej *groupj) |
| void | test_exhaustive_ecmult (const secp256k1_ge *group, const secp256k1_gej *groupj) |
| void | test_exhaustive_ecmult_multi (const secp256k1_context *ctx, const secp256k1_ge *group) |
| void | r_from_k (secp256k1_scalar *r, const secp256k1_ge *group, int k, int *overflow) |
| void | test_exhaustive_verify (const secp256k1_context *ctx, const secp256k1_ge *group) |
| void | test_exhaustive_sign (const secp256k1_context *ctx, const secp256k1_ge *group) |
| int | main (int argc, char **argv) |
Macro Definition Documentation
◆ EXHAUSTIVE_TEST_ORDER
| #define EXHAUSTIVE_TEST_ORDER 13 |
Definition at line 17 of file tests_exhaustive.c.
Function Documentation
◆ ge_equals_ge()
| void ge_equals_ge | ( | const secp256k1_ge * | a, |
| const secp256k1_ge * | b ) |
stolen from tests.c
Definition at line 31 of file tests_exhaustive.c.
31 {
34 return;
35 }
38}
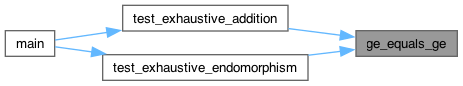
Here is the caller graph for this function:
◆ ge_equals_gej()
| void ge_equals_gej | ( | const secp256k1_ge * | a, |
| const secp256k1_gej * | b ) |
Definition at line 40 of file tests_exhaustive.c.
40 {
41 secp256k1_fe z2s;
42 secp256k1_fe u1, u2, s1, s2;
45 return;
46 }
47 /* Check a.x * b.z^2 == b.x && a.y * b.z^3 == b.y, to avoid inverses. */
48 secp256k1_fe_sqr(&z2s, &b->z);
49 secp256k1_fe_mul(&u1, &a->x, &z2s);
50 u2 = b->x; secp256k1_fe_normalize_weak(&u2);
52 s2 = b->y; secp256k1_fe_normalize_weak(&s2);
53 CHECK(secp256k1_fe_equal_var(&u1, &u2));
54 CHECK(secp256k1_fe_equal_var(&s1, &s2));
55}
Definition field_10x26.h:12
Here is the caller graph for this function:
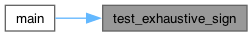
◆ main()
| int main | ( | int | argc, |
| char ** | argv ) |
Definition at line 356 of file tests_exhaustive.c.
356 {
357 int i;
360 unsigned char rand32[32];
361 secp256k1_context *ctx;
362
363 /* Disable buffering for stdout to improve reliability of getting
364 * diagnostic information. Happens right at the start of main because
365 * setbuf must be used before any other operation on the stream. */
366 setbuf(stdout, NULL);
367 /* Also disable buffering for stderr because it's not guaranteed that it's
368 * unbuffered on all systems. */
369 setbuf(stderr, NULL);
370
372
373 /* find iteration count */
374 if (argc > 1) {
376 }
378
379 /* find random seed */
380 secp256k1_testrand_init(argc > 2 ? argv[2] : NULL);
381
382 /* set up split processing */
383 if (argc > 4) {
384 num_cores = strtol(argv[3], NULL, 0);
385 this_core = strtol(argv[4], NULL, 0);
386 if (num_cores < 1 || this_core >= num_cores) {
388 return 1;
389 }
390 printf("running tests for core %lu (out of [0..%lu])\n", (unsigned long)this_core, (unsigned long)num_cores - 1);
391 }
392
393 /* Recreate the ecmult{,_gen} tables using the right generator (as selected via EXHAUSTIVE_TEST_ORDER) */
394 secp256k1_ecmult_gen_compute_table(&secp256k1_ecmult_gen_prec_table[0][0], &secp256k1_ge_const_g, ECMULT_GEN_PREC_BITS);
395 secp256k1_ecmult_compute_two_tables(secp256k1_pre_g, secp256k1_pre_g_128, WINDOW_G, &secp256k1_ge_const_g);
396
397 while (count--) {
398 /* Build context */
400 secp256k1_testrand256(rand32);
402
403 /* Generate the entire group */
404 secp256k1_gej_set_infinity(&groupj[0]);
405 secp256k1_ge_set_gej(&group[0], &groupj[0]);
407 secp256k1_gej_add_ge(&groupj[i], &groupj[i - 1], &secp256k1_ge_const_g);
408 secp256k1_ge_set_gej(&group[i], &groupj[i]);
409 if (count != 0) {
410 /* Set a different random z-value for each Jacobian point, except z=1
411 is used in the last iteration. */
412 secp256k1_fe z;
413 random_fe(&z);
414 secp256k1_gej_rescale(&groupj[i], &z);
415 }
416
417 /* Verify against ecmult_gen */
418 {
419 secp256k1_scalar scalar_i;
420 secp256k1_gej generatedj;
421 secp256k1_ge generated;
422
423 secp256k1_scalar_set_int(&scalar_i, i);
424 secp256k1_ecmult_gen(&ctx->ecmult_gen_ctx, &generatedj, &scalar_i);
425 secp256k1_ge_set_gej(&generated, &generatedj);
426
427 CHECK(group[i].infinity == 0);
431 }
432 }
433
434 /* Run the tests */
435 test_exhaustive_endomorphism(group);
436 test_exhaustive_addition(group, groupj);
437 test_exhaustive_ecmult(group, groupj);
438 test_exhaustive_ecmult_multi(ctx, group);
439 test_exhaustive_sign(ctx, group);
440 test_exhaustive_verify(ctx, group);
441
442#ifdef ENABLE_MODULE_RECOVERY
443 test_exhaustive_recovery(ctx, group);
444#endif
445#ifdef ENABLE_MODULE_EXTRAKEYS
446 test_exhaustive_extrakeys(ctx, group);
447#endif
448#ifdef ENABLE_MODULE_SCHNORRSIG
449 test_exhaustive_schnorrsig(ctx);
450#endif
451
452 secp256k1_context_destroy(ctx);
453 }
454
455 secp256k1_testrand_finish();
456
458 return 0;
459}
LOGGING_API void printf(Category category, const char *format,...)
Definition Logging.cpp:30
const secp256k1_ge_storage secp256k1_pre_g_128[ECMULT_TABLE_SIZE(WINDOW_G)]
Definition precomputed_ecmult.c:8240
const secp256k1_ge_storage secp256k1_pre_g[ECMULT_TABLE_SIZE(WINDOW_G)]
Definition precomputed_ecmult.c:20
const secp256k1_ge_storage secp256k1_ecmult_gen_prec_table[ECMULT_GEN_PREC_N(ECMULT_GEN_PREC_BITS)][ECMULT_GEN_PREC_G(ECMULT_GEN_PREC_BITS)]
Definition precomputed_ecmult_gen.c:14
SECP256K1_API void secp256k1_context_destroy(secp256k1_context *ctx) SECP256K1_ARG_NONNULL(1)
Definition secp256k1.c:146
SECP256K1_API SECP256K1_WARN_UNUSED_RESULT int secp256k1_context_randomize(secp256k1_context *ctx, const unsigned char *seed32) SECP256K1_ARG_NONNULL(1)
Definition secp256k1.c:706
SECP256K1_API secp256k1_context * secp256k1_context_create(unsigned int flags) SECP256K1_WARN_UNUSED_RESULT
Definition secp256k1.c:107
Definition secp256k1.c:47
secp256k1_ecmult_gen_context ecmult_gen_ctx
Definition secp256k1.c:48
Definition group.h:16
Definition group.h:28
Definition scalar_4x64.h:13
void test_exhaustive_ecmult_multi(const secp256k1_context *ctx, const secp256k1_ge *group)
Definition tests_exhaustive.c:202
void test_exhaustive_ecmult(const secp256k1_ge *group, const secp256k1_gej *groupj)
Definition tests_exhaustive.c:166
void test_exhaustive_sign(const secp256k1_context *ctx, const secp256k1_ge *group)
Definition tests_exhaustive.c:295
void test_exhaustive_addition(const secp256k1_ge *group, const secp256k1_gej *groupj)
Definition tests_exhaustive.c:106
void test_exhaustive_verify(const secp256k1_context *ctx, const secp256k1_ge *group)
Definition tests_exhaustive.c:242
void test_exhaustive_endomorphism(const secp256k1_ge *group)
Definition tests_exhaustive.c:97
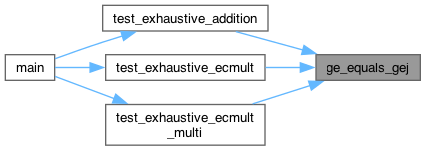
Here is the call graph for this function:
◆ r_from_k()
| void r_from_k | ( | secp256k1_scalar * | r, |
| const secp256k1_ge * | group, | ||
| int | k, | ||
| int * | overflow ) |
Definition at line 232 of file tests_exhaustive.c.
232 {
233 secp256k1_fe x;
234 unsigned char x_bin[32];
235 k %= EXHAUSTIVE_TEST_ORDER;
236 x = group[k].x;
237 secp256k1_fe_normalize(&x);
238 secp256k1_fe_get_b32(x_bin, &x);
240}
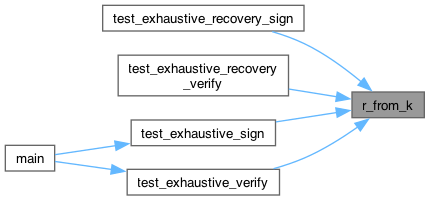
Here is the caller graph for this function:
◆ random_fe()
| void random_fe | ( | secp256k1_fe * | x | ) |
Definition at line 57 of file tests_exhaustive.c.
57 {
58 unsigned char bin[32];
59 do {
60 secp256k1_testrand256(bin);
61 if (secp256k1_fe_set_b32(x, bin)) {
62 return;
63 }
64 } while(1);
65}
Here is the caller graph for this function:
◆ secp256k1_nonce_function_smallint()
| int secp256k1_nonce_function_smallint | ( | unsigned char * | nonce32, |
| const unsigned char * | msg32, | ||
| const unsigned char * | key32, | ||
| const unsigned char * | algo16, | ||
| void * | data, | ||
| unsigned int | attempt ) |
Definition at line 77 of file tests_exhaustive.c.
79 {
81 int *idata = data;
82 (void)msg32;
83 (void)key32;
84 (void)algo16;
85 /* Some nonces cannot be used because they'd cause s and/or r to be zero.
86 * The signing function has retry logic here that just re-calls the nonce
87 * function with an increased `attempt`. So if attempt > 0 this means we
88 * need to change the nonce to avoid an infinite loop. */
89 if (attempt > 0) {
90 *idata = (*idata + 1) % EXHAUSTIVE_TEST_ORDER;
91 }
92 secp256k1_scalar_set_int(&s, *idata);
93 secp256k1_scalar_get_b32(nonce32, &s);
94 return 1;
95}
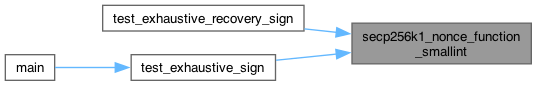
Here is the caller graph for this function:
◆ test_exhaustive_addition()
| void test_exhaustive_addition | ( | const secp256k1_ge * | group, |
| const secp256k1_gej * | groupj ) |
Definition at line 106 of file tests_exhaustive.c.
106 {
108 uint64_t iter = 0;
109
110 /* Sanity-check (and check infinity functions) */
111 CHECK(secp256k1_ge_is_infinity(&group[0]));
112 CHECK(secp256k1_gej_is_infinity(&groupj[0]));
114 CHECK(!secp256k1_ge_is_infinity(&group[i]));
115 CHECK(!secp256k1_gej_is_infinity(&groupj[i]));
116 }
117
118 /* Check all addition formulae */
120 secp256k1_fe fe_inv;
121 if (skip_section(&iter)) continue;
122 secp256k1_fe_inv(&fe_inv, &groupj[j].z);
124 secp256k1_ge zless_gej;
125 secp256k1_gej tmp;
126 /* add_var */
127 secp256k1_gej_add_var(&tmp, &groupj[i], &groupj[j], NULL);
129 /* add_ge */
131 secp256k1_gej_add_ge(&tmp, &groupj[i], &group[j]);
133 }
134 /* add_ge_var */
135 secp256k1_gej_add_ge_var(&tmp, &groupj[i], &group[j], NULL);
137 /* add_zinv_var */
141 secp256k1_gej_add_zinv_var(&tmp, &groupj[i], &zless_gej, &fe_inv);
143 }
144 }
145
146 /* Check doubling */
148 secp256k1_gej tmp;
149 secp256k1_gej_double(&tmp, &groupj[i]);
151 secp256k1_gej_double_var(&tmp, &groupj[i], NULL);
153 }
154
155 /* Check negation */
157 secp256k1_ge tmp;
158 secp256k1_gej tmpj;
159 secp256k1_ge_neg(&tmp, &group[i]);
161 secp256k1_gej_neg(&tmpj, &groupj[i]);
163 }
164}
void ge_equals_ge(const secp256k1_ge *a, const secp256k1_ge *b)
Definition tests_exhaustive.c:31
void ge_equals_gej(const secp256k1_ge *a, const secp256k1_gej *b)
Definition tests_exhaustive.c:40
Here is the call graph for this function:
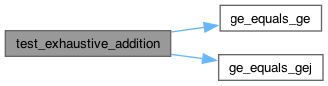
Here is the caller graph for this function:
◆ test_exhaustive_ecmult()
| void test_exhaustive_ecmult | ( | const secp256k1_ge * | group, |
| const secp256k1_gej * | groupj ) |
Definition at line 166 of file tests_exhaustive.c.
166 {
168 uint64_t iter = 0;
171 if (skip_section(&iter)) continue;
173 secp256k1_gej tmp;
174 secp256k1_scalar na, ng;
175 secp256k1_scalar_set_int(&na, i);
176 secp256k1_scalar_set_int(&ng, j);
177
178 secp256k1_ecmult(&tmp, &groupj[r_log], &na, &ng);
180
181 if (i > 0) {
182 secp256k1_ecmult_const(&tmp, &group[i], &ng, 256);
184 }
185 }
186 }
187 }
188}
Here is the call graph for this function:
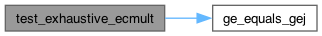
Here is the caller graph for this function:
◆ test_exhaustive_ecmult_multi()
| void test_exhaustive_ecmult_multi | ( | const secp256k1_context * | ctx, |
| const secp256k1_ge * | group ) |
Definition at line 202 of file tests_exhaustive.c.
202 {
204 uint64_t iter = 0;
210 if (skip_section(&iter)) continue;
212 secp256k1_gej tmp;
213 secp256k1_scalar g_sc;
214 ecmult_multi_data data;
215
216 secp256k1_scalar_set_int(&data.sc[0], i);
217 secp256k1_scalar_set_int(&data.sc[1], j);
218 secp256k1_scalar_set_int(&g_sc, k);
219 data.pt[0] = group[x];
220 data.pt[1] = group[y];
221
222 secp256k1_ecmult_multi_var(&ctx->error_callback, scratch, &tmp, &g_sc, ecmult_multi_callback, &data, 2);
224 }
225 }
226 }
227 }
228 }
229 secp256k1_scratch_destroy(&ctx->error_callback, scratch);
230}
Definition tests.c:4022
Definition scratch.h:12
Here is the call graph for this function:
Here is the caller graph for this function:
◆ test_exhaustive_endomorphism()
| void test_exhaustive_endomorphism | ( | const secp256k1_ge * | group | ) |
Definition at line 97 of file tests_exhaustive.c.
Here is the call graph for this function:
Here is the caller graph for this function:
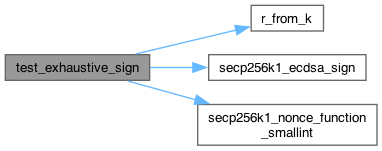
◆ test_exhaustive_sign()
| void test_exhaustive_sign | ( | const secp256k1_context * | ctx, |
| const secp256k1_ge * | group ) |
Definition at line 295 of file tests_exhaustive.c.
295 {
297 uint64_t iter = 0;
298
299 /* Loop */
302 if (skip_section(&iter)) continue;
304 const int starting_k = k;
306 secp256k1_ecdsa_signature sig;
308 unsigned char sk32[32], msg32[32];
309 secp256k1_scalar_set_int(&msg, i);
310 secp256k1_scalar_set_int(&sk, j);
311 secp256k1_scalar_get_b32(sk32, &sk);
312 secp256k1_scalar_get_b32(msg32, &msg);
313
316
318 /* Note that we compute expected_r *after* signing -- this is important
319 * because our nonce-computing function function might change k during
320 * signing. */
321 r_from_k(&expected_r, group, k, NULL);
324 (k * (EXHAUSTIVE_TEST_ORDER - s)) % EXHAUSTIVE_TEST_ORDER == (i + r * j) % EXHAUSTIVE_TEST_ORDER);
325
326 /* Overflow means we've tried every possible nonce */
327 if (k < starting_k) {
328 break;
329 }
330 }
331 }
332 }
333
334 /* We would like to verify zero-knowledge here by counting how often every
335 * possible (s, r) tuple appears, but because the group order is larger
336 * than the field order, when coercing the x-values to scalar values, some
337 * appear more often than others, so we are actually not zero-knowledge.
338 * (This effect also appears in the real code, but the difference is on the
339 * order of 1/2^128th the field order, so the deviation is not useful to a
340 * computationally bounded attacker.)
341 */
342}
SECP256K1_API int secp256k1_ecdsa_sign(const secp256k1_context *ctx, secp256k1_ecdsa_signature *sig, const unsigned char *msghash32, const unsigned char *seckey, secp256k1_nonce_function noncefp, const void *ndata) SECP256K1_ARG_NONNULL(1) SECP256K1_ARG_NONNULL(2) SECP256K1_ARG_NONNULL(3) SECP256K1_ARG_NONNULL(4)
Definition secp256k1.c:514
Definition secp256k1.h:83
int secp256k1_nonce_function_smallint(unsigned char *nonce32, const unsigned char *msg32, const unsigned char *key32, const unsigned char *algo16, void *data, unsigned int attempt)
Definition tests_exhaustive.c:77
void r_from_k(secp256k1_scalar *r, const secp256k1_ge *group, int k, int *overflow)
Definition tests_exhaustive.c:232
Here is the call graph for this function:
Here is the caller graph for this function:
◆ test_exhaustive_verify()
| void test_exhaustive_verify | ( | const secp256k1_context * | ctx, |
| const secp256k1_ge * | group ) |
Definition at line 242 of file tests_exhaustive.c.
242 {
244 uint64_t iter = 0;
249 secp256k1_ge nonconst_ge;
250 secp256k1_ecdsa_signature sig;
251 secp256k1_pubkey pk;
252 secp256k1_scalar sk_s, msg_s, r_s, s_s;
253 secp256k1_scalar s_times_k_s, msg_plus_r_times_sk_s;
254 int k, should_verify;
255 unsigned char msg32[32];
256
257 if (skip_section(&iter)) continue;
258
259 secp256k1_scalar_set_int(&s_s, s);
260 secp256k1_scalar_set_int(&r_s, r);
261 secp256k1_scalar_set_int(&msg_s, msg);
262 secp256k1_scalar_set_int(&sk_s, key);
263
264 /* Verify by hand */
265 /* Run through every k value that gives us this r and check that *one* works.
266 * Note there could be none, there could be multiple, ECDSA is weird. */
267 should_verify = 0;
269 secp256k1_scalar check_x_s;
270 r_from_k(&check_x_s, group, k, NULL);
271 if (r_s == check_x_s) {
272 secp256k1_scalar_set_int(&s_times_k_s, k);
273 secp256k1_scalar_mul(&s_times_k_s, &s_times_k_s, &s_s);
274 secp256k1_scalar_mul(&msg_plus_r_times_sk_s, &r_s, &sk_s);
275 secp256k1_scalar_add(&msg_plus_r_times_sk_s, &msg_plus_r_times_sk_s, &msg_s);
276 should_verify |= secp256k1_scalar_eq(&s_times_k_s, &msg_plus_r_times_sk_s);
277 }
278 }
279 /* nb we have a "high s" rule */
280 should_verify &= !secp256k1_scalar_is_high(&s_s);
281
282 /* Verify by calling verify */
283 secp256k1_ecdsa_signature_save(&sig, &r_s, &s_s);
285 secp256k1_pubkey_save(&pk, &nonconst_ge);
286 secp256k1_scalar_get_b32(msg32, &msg_s);
287 CHECK(should_verify ==
288 secp256k1_ecdsa_verify(ctx, &sig, msg32, &pk));
289 }
290 }
291 }
292 }
293}
SECP256K1_API SECP256K1_WARN_UNUSED_RESULT int secp256k1_ecdsa_verify(const secp256k1_context *ctx, const secp256k1_ecdsa_signature *sig, const unsigned char *msghash32, const secp256k1_pubkey *pubkey) SECP256K1_ARG_NONNULL(1) SECP256K1_ARG_NONNULL(2) SECP256K1_ARG_NONNULL(3) SECP256K1_ARG_NONNULL(4)
Definition secp256k1.c:400
Definition secp256k1.h:70
memcpy((char *) pInfo->slotDescription, s, l)
Here is the call graph for this function:
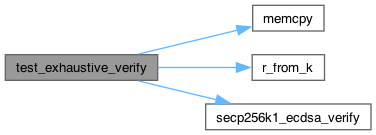
Here is the caller graph for this function: